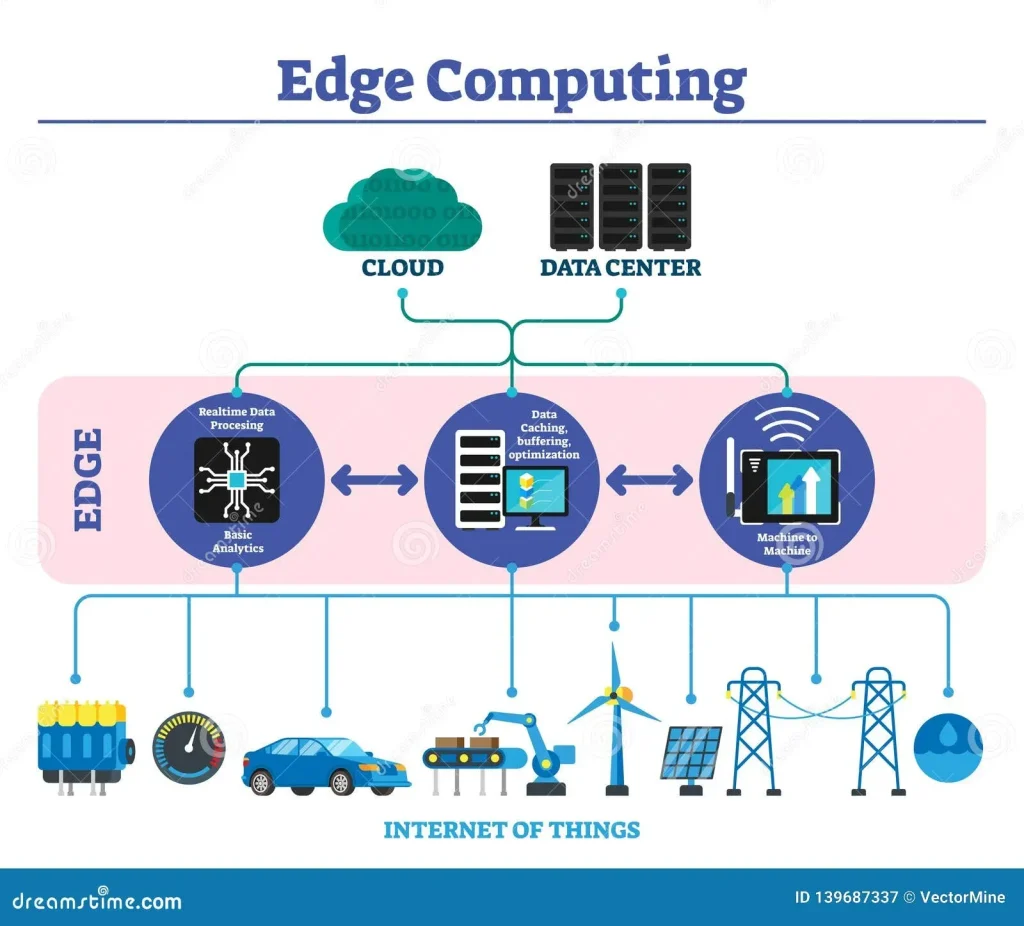
Edge Computing Technology is redefining how organizations process data at the source, bringing computation closer to where it’s generated. This approach reduces latency, lowers bandwidth use, and unlocks real-time insights across edge computing use cases in manufacturing, healthcare, and smart cities. This accelerates the edge computing benefits by enabling real-time actions on data at the source, using edge devices and IoT. Choosing between edge vs cloud computing requires understanding where latency matters most and how data flows from the edge to centralized data centers. Overall, edge security, scalable edge architectures, and intelligent local processing define the future of interoperable, efficient enterprise IT.
Think of this as near-edge processing, where computation, storage, and AI inference occur on devices, gateways, or micro data centers close to the data source. This distributed architecture mirrors concepts like local analytics, on-device processing, and proximity computing, delivering low-latency responses without constantly pinging centralized clouds. By emphasizing data locality and offline capability, organizations can maintain operation during network disruptions while preserving privacy. As technologies evolve, this ecosystem integrates with 5G, edge security, and interoperable platforms to create a resilient, intelligent fabric for modern applications.
Edge Computing Technology: Enabling Ultra-Low Latency and Secure AI at the Edge
Edge Computing Technology sits at the core of modern data processing, bringing compute power and analytics directly to where data is generated. By moving processing to the network edge, organizations can achieve ultra-low latency, reduce dependence on central data centers, and unlock real-time insights that support faster decision-making. This proximity to data sources also helps conserve bandwidth, as only relevant results and insights are transmitted rather than continuous streams of raw data. The result is a more responsive, resilient, and privacy-conscious approach to IT that aligns with enterprise goals for speed and control.
In practice, Edge Computing Technology enables a variety of edge computing use cases across industries—manufacturing, healthcare, retail, and smart cities—where milliseconds matter. This is complemented by edge devices and IoT that generate data at the edge and perform local inference or aggregation, reducing the need to shuttle sensitive information to the cloud. Emphasizing edge security and governance from the outset ensures that local data stays within defined boundaries, while AI at the edge delivers timely insights with minimal bandwidth usage and enhanced privacy.
Edge Use Cases, Security, and Hybrid Architectures: Strategic Deployment for Real-World Results
A practical edge strategy links diverse edge computing use cases to hybrid cloud patterns. Latency-sensitive workloads—such as autonomous systems, real-time monitoring, and industrial control—are deployed at the edge, while batch analytics, long-term storage, and expansive data science are handled in the cloud. This edge vs cloud computing balance reduces round-trip times, optimizes bandwidth, and creates a scalable, resilient architecture that can adapt as data volumes grow and business needs evolve.
To turn strategy into reliable operations, organizations should emphasize edge security, ongoing updates, and interoperable architectures. A robust approach combines hardware-based security with software governance, secure boot, encryption, and continuous monitoring across distributed devices. Practices like modular deployment, remote management of edge devices, and consideration of edge devices and IoT ecosystems help ensure data governance, compliance, and seamless synchronization between the edge and the cloud for consistent insights.
Frequently Asked Questions
What are some common edge computing use cases that illustrate the benefits of edge computing technology?
Common edge computing use cases span manufacturing, retail, healthcare, and smart cities, where data is processed near its source to unlock real-time insights. By running AI inference, anomaly detection, and local analytics on edge devices and gateways, organizations achieve lower latency, reduced bandwidth requirements, and offline resilience. This edge-focused approach benefits from edge devices and IoT ecosystems, enabling faster responses while maintaining privacy and governance.
How should organizations compare edge vs cloud computing when planning latency-sensitive workloads?
Edge vs cloud computing is not a choice between two separate worlds but a complementary mix. Placing latency-sensitive workloads at the edge reduces round-trip time for real-time analytics, while batch processing and long-term storage stay in the cloud. A well-governed hybrid architecture with clear workload placement, data synchronization, and a focus on edge security ensures consistent results across on-premises devices, gateways, and cloud services.
| Topic | Key Point | Summary |
|---|---|---|
| Definition | What is Edge Computing Technology | Edge Computing Technology processes data at or near the data source—on devices, gateways, or micro data centers at the network edge—reducing distance, latency, and bandwidth needs. |
| Why it matters | Core benefits | Enables real-time decisions, reduces data movement, preserves privacy, and improves system resilience by supporting offline or intermittent operation. |
| Key Benefits | Overview | Reduced latency; Bandwidth optimization; Improved data privacy and sovereignty; Enhanced reliability and offline operation; Scalable, distributed architectures; Contextual insights and personalization. |
| Use Cases | Industries and scenarios | Manufacturing (predictive maintenance, real-time quality), Retail (on-site analytics, personalized experiences), Healthcare (rapid alerts with privacy), Smart cities (traffic, environmental monitoring), Logistics, Energy, Agriculture (distributed optimization). |
| Edge Devices and IoT | Devices | Ranging from microcontrollers to industrial gateways and edge servers; IoT platforms collect data, while edge devices compute locally to speed responses and improve privacy. |
| Security at the Edge | Security approach | Layered defenses across hardware and software; secure boot; encryption; access controls; secure firmware updates; continuous monitoring and anomaly detection. |
| Edge vs Cloud | Relationship | Not mutually exclusive; hybrid model where latency-sensitive workloads run at the edge and batch analytics or long-term storage in the cloud; requires governance and synchronization. |
| Implementation & Best Practices | Guidelines | Use-case-driven approach; modular, scalable design; standardization; invest in edge security; governance and data lineage; maintenance and remote updates; edge AI where suitable; managed edge services. |
| Future Trends | Outlook | More on-device AI acceleration; smaller, energy-efficient edge devices; more micro data centers; closer 5G integration; standardized security models; convergence with digital twins, AR, and real-time decision-making. |
Summary
Conclusion